Hi, I’m Dhruvesh Panchal
a Cyber Crime Investigator.
a Data Recovery Expert.
an Author.
an Ethical Hacker.
a Cyber Expert.
“At 13, while others were playing games… I was exploring systems to understand how they work.” This is my journey — I’m Dhruvesh Panchal, now focused on securing the digital world with the same curiosity.
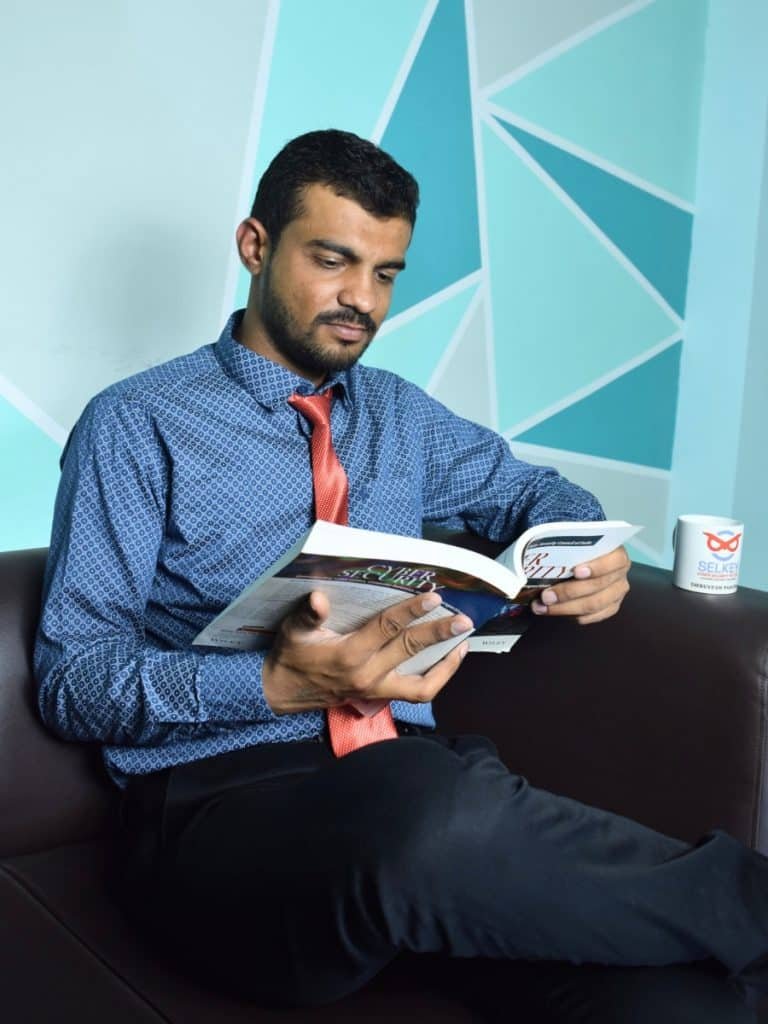
Dhruvesh Panchal
Ethical Hacker | Cyber Expert
Cyber Crime Investigator | PhD (P.) M.Sc.(CSDF) | B.com | CPT | IGDCSE
CEH (Master) | CNDA | EHCSE | PTSA SCSP | ISO 27001:2013 Lead Auditor
Dhruvesh Panchal
I’m Dhruvesh Panchal, a cybersecurity professional passionate about protecting digital systems and promoting online safety.
My journey began at the age of 13, driven by a deep curiosity to understand how systems function and where vulnerabilities exist. Over time, this curiosity evolved into strong expertise in ethical hacking and cybersecurity. I was honored to receive a gold medal in a hacking course from Gujarat University, reflecting my dedication and technical proficiency.
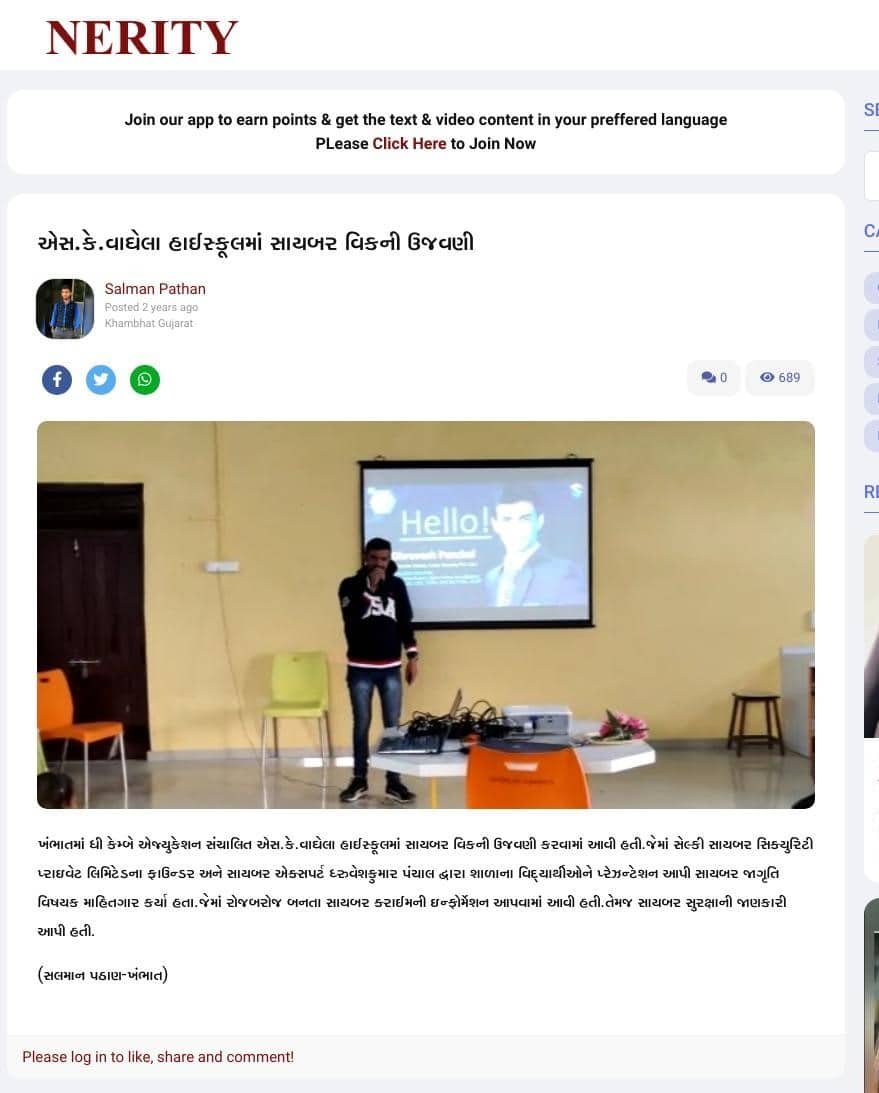
Beyond my technical work, I actively conduct seminars and awareness programs—especially for students—to educate them about cyber threats, safe online practices and the importance of ethical hacking. I believe cybersecurity is not just about solving problems, but preventing them and building a safer digital future for everyone.
I am continuously learning and adapting to the ever-evolving cyber landscape, ensuring that my knowledge and skills remain up to date. My focus is on delivering practical solutions, raising awareness and contributing toward a more secure and responsible digital ecosystem.
I strive to make cybersecurity simple, accessible and impactful for individuals as well as organizations. My mission is to not only secure systems but also to inspire others to explore cybersecurity with the right knowledge and ethical mindset.
Data Recovery Expert
Cyber Crime Investigator
Cyber Expert
Ethical Hacker
Data Recovery Expert
Cyber Crime Investigator
Cyber Expert
Ethical Hacker
WHAT I DO
Beyond investigations, he is committed to building a safer digital society. Through seminars, workshops, and NGO-led initiatives, he spreads awareness about cybercrime, online scams and digital safety—especially among students and young users.
A gold medalist from Gujarat University, Dhruvesh combines technical excellence with a mission-driven approach, focusing not just on solving cyber issues, but preventing them and empowering individuals with the knowledge to stay secure.
Cybercrime Case Solving
Investigating cyber incidents, tracing digital evidence and resolving cybercrime cases through ethical hacking and advanced forensic analysis.
Cybersecurity Leadership
Driving cybersecurity strategies and awareness initiatives to protect organizations from evolving digital threats.
Awareness & Education
Educating students and organizations about cyber threats and empowering them with practical knowledge to stay secure online.
Scam Prevention & Digital Safety
Protecting users from online fraud by providing practical strategies for scam prevention and digital security.
Empowering the Next Generation
Mentoring students and aspiring professionals to build strong skills in cybersecurity and ethical hacking.
Achievements & Vision
Building on past experience to drive stronger cybersecurity practices and enhance digital resilience for the future.
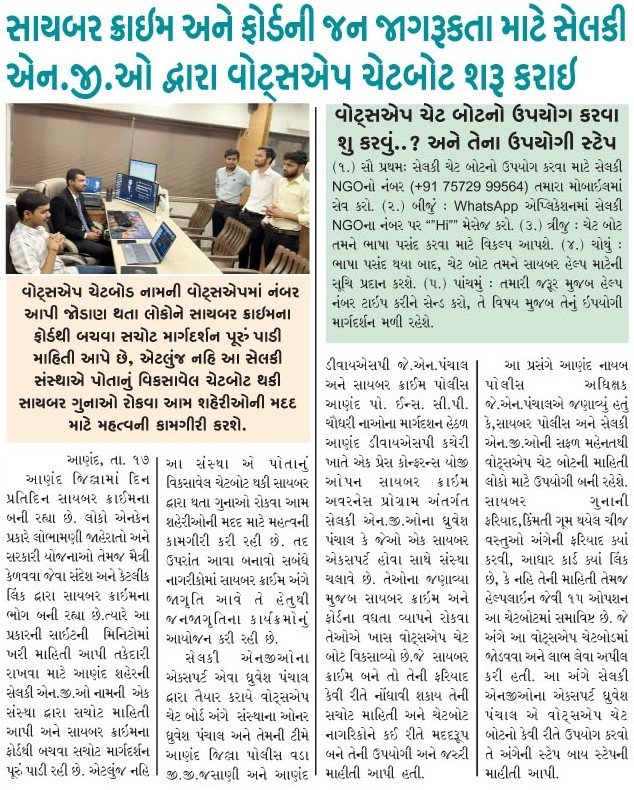
Selkey NGO
At Selkey Cyber Security, we are proud to introduce Selkey NGO—an initiative focused on empowering communities through cyber awareness. In today’s digital age, staying secure online is essential, and through this initiative, we educate individuals about cyber threats, promote safe digital practices and provide practical knowledge through workshops, seminars and webinars for all age groups. Our aim is to build a more informed, responsible and secure digital society where everyone can confidently navigate the online world.
Selkey Cyber Security Pvt Ltd
Selkey Cyber Security Private Limited was established in 2022 with a mission to secure and strengthen digital operations. We offer a comprehensive range of services including cybersecurity, web development, cloud security, penetration testing, data recovery and infrastructure security. By combining industry expertise with advanced technologies, we help protect digital assets, minimize risks and support business growth in an increasingly digital world. Our approach focuses on delivering customized solutions, reliable strategies and proactive support to ensure your systems remain secure, efficient and resilient.
Awesome Clients































































Workshop Overview
Selkey NGO, established under Selkey Cyber Security Pvt. Ltd., is dedicated to combating the rise of cyber fraud and creating widespread digital awareness. The initiative focuses on building a secure digital environment by conducting workshops, seminars and awareness campaigns across schools, colleges, institutions and organizations, educating individuals about online threats and safe practices. Beyond education, the NGO also supports and guides victims of cybercrime through recovery processes, offering lawful solutions and assistance. With impactful initiatives, including awareness programs at Cambay ONGC and other successful projects, Selkey NGO continues to lead efforts in promoting cybersecurity awareness. Its vision is to create a safer, more informed society where individuals can confidently navigate their digital lives.
Workshop Overview
Selkey Cyber Security Pvt. Ltd. delivers advanced cybersecurity solutions designed to protect individuals, businesses and institutions from evolving digital threats. Our services include threat assessment, penetration testing, vulnerability management and cybersecurity consulting, all executed with high security standards and full compliance. In addition to technical services, we provide training and resources to help clients maintain a secure digital presence, while also driving NGO initiatives focused on cyber fraud prevention and awareness. With impactful programs such as cyber awareness sessions at Cambay ONGC, we combine innovation and professionalism to build a secure, resilient and future-ready digital ecosystem.






Data Recovery Expert
Cyber Crime Investigator
Cyber Expert
Ethical Hacker
Data Recovery Expert
Cyber Crime Investigator
Cyber Expert
Ethical Hacker
Testimonial
Testimonial
@Arjun Singh CTO at SecureTech Inc.
Working with Dhruvesh Panchal was an eye-opening experience. As a Cyber Expert and Ethical Hacker, he identified and fixed critical vulnerabilities in our systems. His attention to detail and ethical approach are unmatched. I highly recommend him for cybersecurity services!
@Meera Desai IT Manager
Thanks to Dhruvesh Panchal, our system vulnerabilities were fixed, and we now feel secure. Highly recommend his services!
@Priya Sharma Online Entrepreneur
Dhruvesh Panchal quickly identified and helped resolve an online scam I was a victim of. Highly professional!
@Vikram Rao Graphic Designer
Incredible! Dhurvesh Panchal recovered 98% of my lost data after my hard drive crash. Highly skilled!""Incredible! Dhurvesh Panchal recovered 98% of my lost data after my hard drive crash. Highly skilled!
My Blog
Who is Dhruvesh Panchal
Journey of a Cybersecurity Expert & Ethical Hacker
In the modern and ever-changing digital environment, cybersecurity has become an essential field in the world. As technology usage grows in society, so do risks in terms of cyber threats, hacking attempts, data breaches, and online frauds. People, organizations, and even governments look for ways to protect their digital presence in society. In this sense, cybersecurity experts play an important role in building a secure digital environment that users can trust. My personal journey as an ethical hacker and cybersecurity expert was driven by this idea: contributing to the creation of a secure digital environment.
From an early stage in my life, I have been aware of the fact that my interest in technology has been different from that of most of my peers. For instance, while most of them have been using technology in a superficial way, such as using smartphones, accessing the internet, and engaging in various forms of social media, I have been driven by the need to understand the mechanisms of technology. For instance, I have been driven by the need to understand how websites are developed, how servers interact with each other, and, most fundamentally, how these technologies are secured. This was not just a fleeting interest but rather developed into a lifelong quest for knowledge, which ultimately led to the field of cybersecurity.
My introduction to ethical hacking began at a relatively early stage in my development. At a point in life where many people are still in the process of discovering their interests and passions, I began to study the vulnerabilities of systems and the process of cyberattacks. The focus of my study was concentrated around the fundamental concepts of cybersecurity, including network security, system vulnerabilities, and penetration testing. As I continued to learn more about the process, I began to clarify the way in which attackers utilize the system vulnerabilities and the way in which they could be identified and addressed. A defining moment in my early development came in the form of the choice that I made to pursue the route of ethical hacking. Rather than using the knowledge and skills that I had developed for negative purposes, I chose to utilize them in a positive way, helping people and organizations to protect themselves against attacks.
With my progression in my professional path, I have continued to expand my knowledge base in various fields within the realm of cybersecurity. This included the pursuit of knowledge in the field of web application security, vulnerability assessments, ethical hacking techniques, and cyber threats. Again, there was a focus on learning through practice, given the importance of learning in the real world. I have been able to develop the ability to effectively learn how to analyse a system, identify the risks, and develop appropriate measures to mitigate those risks.
As I continued to gain more experience, I was able to apply my knowledge in real-world situations. I was actively engaged in identifying security threats, contributing to the solution of security issues related to cybersecurity, and offering guidance on how to approach security in digital situations. As I continued to gain more experience in analysing complex situations and identifying potential security threats, I was recognized in the cybersecurity field. This was an important part of my professional development and helped me gain more confidence in handling real-world problems.
In order to expand my impact and reach a wider audience,
I founded Selkey Cyber Security Pvt Ltd.
The aim through this platform was to offer structured cybersecurity solutions, promote ethical hacking practices, and assist people and organizations in developing more effective cybersecurity strategies. Establishing this platform enabled me to organize my knowledge and experience in a manner that could be more impactful on a wider audience. My aim was to develop a digital environment where people could utilize technology without fear.
Aside from my professional role, I argue that awareness represents a highly influential tool for the prevention of cybercrime. A huge percentage of cybercrimes does not result from sophisticated cyberattacks, but rather from a lack of user awareness. In this context, I have actively participated in enhancing user awareness with regard to cybersecurity through the Selkey NGO.
The goal of my efforts is to empower users, be it students, professionals, or simply citizens, through a series of workshops, seminars, and awareness programs with regard to cybersecurity. The goal is not simply to raise users’ awareness, but to empower users with regard to their own protection within the digital world.
In addition to this, I am also highly committed to developing the next generation of cybersecurity experts. I provide training sessions, workshops, and mentorship to young and aspiring ethical hackers. My teaching philosophy goes beyond mere knowledge and skill acquisition in this field; I also focus on the ethical and appropriate use of this knowledge. I firmly believe that knowledge in this field must be used to harm and not to heal. From all my experiences, I hope to assist students and professionals in developing a foundational knowledge base in this field and to pursue it as a career.
One of the major factors that have influenced my professional path is my mindset. Cybersecurity is a dynamic field where new challenges are emerging every day. To remain relevant in the field, it is essential to keep learning. I always emphasize the importance of staying up to date with the latest trends and technologies in the cybersecurity domain. My inspiration is driven by curiosity, discipline, and a commitment to ethics. To me, ethical hacking is more than just finding vulnerabilities; it is protecting people, building trust, and creating a safer cyber world.
Looking forward, the aim is to continue further contributions to the field of cybersecurity. This includes broadening the reach through awareness, creating advanced security measures, and training more people to become competent ethical hackers. With technology advancing further, there will also be a growing need for cybersecurity, and the aim is to take part in this evolution. The end goal is to create a digital world where people are not only protected but also aware of how to protect themselves.
Throughout my experience in cybersecurity, the guiding principles have been inquiry, learning, and a strong feeling of responsibility. From initial exploration and discovery of technology to creating a professional presence within the cybersecurity domain, every step has offered instructional learnings. It is my belief that success in cybersecurity is not just about having the requisite skill set, but about leveraging the skill set to produce a positive effect. For those looking to pursue a career in cybersecurity, my experience has taught me that it is possible to build a meaningful and impactful presence in the field.
My Daily Routine as a Cybersecurity Expert
For a cybersecurity domain, it can be stated that day-to-day conditions are varied and non-identical. Each day brings its own set of challenges and opportunities for further learning. One of the common questions would be about the nature of a typical day for a cybersecurity expert. The answer would be that there is no particular pattern, but over a period of time, I, Dhruvesh Panchal, have developed a methodology for productivity and focus in this dynamic domain.
My day starts early. I strongly believe that the start to a day determines the nature and pace of all activities that follow. I choose to start my day with a clear mind, without immediately engaging myself in any activity or distraction. This time helps me to mentally prepare for the day that is to come. Starting a day with a clear mind is important, especially for a domain such as cybersecurity, where concentration is required.
Another one of my initial practices is to stay abreast of the latest developments in the world of cybersecurity. Due to the fast-paced nature of this industry, it is vital to stay informed about what is happening on a global scale, especially with regard to emerging vulnerabilities, new types of attacks and novel forms of cybersecurity. One must develop the discipline to read articles about what is going on in the world of cybersecurity.

Subsequently, I move on to carry out my core professional activities. This segment of the day is dedicated to carrying out activities related to cybersecurity, which may include analysis, identification or even the exploration of various security concerns. Each task demands high levels of concentration and a problem-solving approach. Each problem is addressed with scholarly interest and my objective is to comprehend not only the problem itself but also the rationale for the problem.
A considerable part of my daily routine involves constant education. Despite how experienced one might be, there are always new developments in cybersecurity. I dedicate time each day to studying, whether it be exploring a newly introduced tool, explaining a concept I am unfamiliar with or practicing various techniques. I believe this constant education has been one of the major contributors to my growth. I do not consider learning a separate activity; rather, I consider it a part of my daily routine.
Practice is another key component of my daily routine. Ethical hacking is a skill set and it is improved upon through practice. I make sure I practice different scenarios, which in turn increases my knowledge in the real world. I have noticed that the only way knowledge can be turned into expertise is through practice.
In order to expand my impact and reach a wider audience, I founded Selkey Cyber Security Pvt Ltd.
Effective time management is an important part of my daily routine. Since I have a variety of tasks, it can be difficult to stay focused and avoid distractions. However, I prioritize tasks and try to focus on those that are most important. This helps me avoid unnecessary distractions and stay disciplined, thereby ensuring proper time management.
Besides my technical contributions, I am dedicated to the dissemination of knowledge. Through interactions like workshops, seminars and others, I remain dedicated to giving back to my community. The process of giving back to others through teachings and mentorship not only helps them advance, but it also helps me advance my own knowledge. The process of communicating ideas in an easy-to-understand manner requires precision and this process helps me advance my own knowledge.
Another important element that is a part of my routine is ensuring that the right mental state is achieved. It is a highly stressful domain, especially when dealing with complex issues. It is important to ensure that one remains calm and patient. Thus, a balanced mental state is as important as possessing the right skillset for this particular domain.
Physical and mental well-being are part of my daily routines. It is tiring to be exposed to screen time for an extended period. I address this by taking care of my health through regular breaks, exercise and rest. These small actions help me stay energized throughout my day.
At the end of the day, I practice self-reflection. During this time, I evaluate my learning, my achievements and my areas of improvement. This self-reflection ensures that I am aware of my progress and helps me to better plan for the next day. This practice also gives me a sense of direction and purpose.
One thing that was realized over the course of time is that being consistent is more important than being intense. There is no need to complete all the tasks at the same time, but consistent efforts are required on a daily basis. The efforts, although small, add up to give significant results.
For individuals seeking a career in the field of cybersecurity, a well-structured routine may prove to be a significant performance booster. This is because a routine helps an individual focus, manage time and continue to improve professionally. However, at the same time, one must also be flexible, especially because the field is constantly changing.
While my daily routine includes activities beyond just work, they are centred around growth, learning and improvement. Similarly, while cybersecurity is a career for me, it is also a path that changes and evolves over time.
Skills You Need to Become an Ethical Hacker
To become an ethical hacker, one must move beyond the knowledge of a limited set of tools or techniques, but rather develop a holistic mindset, create a strong skill set and gain a comprehensive understanding of the operational dynamics of computing systems. While commencing one’s journey in the domain of cybersecurity, it may not be clear what specific set of skills an individual must possess in order to become an effective ethical hacker. Instead, one discovers what these are through the process of exploration, experimentation and experience. Currently, I, Dhruvesh Panchal, plan to specify the set of skills which I believe are critical in helping an individual become a successful ethical hacker.
The first and most important competency to understand and master is curiosity. Before one even begins to delve into technical matters, one has to first cultivate a mindset that embodies inquiry and questions. Ethical hacking begins with questions of how and why. How does a certain system operate? Why does a certain vulnerability exist? Without a sense of curiosity, one can never hope to reach a certain depth in terms of mastering and comprehending matters related to cyber security. For me, curiosity has been the main driving force behind learning and discovering areas often ignored by others.

The second important skill is a strong understanding of computer networks. It is important to note that cybersecurity is, in itself, closely related to the nature of communication within computer systems. It is important to have a basic understanding of concepts such as IP addresses, DNS, HTTP/HTTPS and firewalls. While computer networks may appear to be a complex concept, the underlying concepts make subsequent concepts of cybersecurity easy to comprehend. The concept of computer networks was a turning point for me.
Another important skill to learn is basic programming skills. You do not necessarily need to be a programmer, but having a basic idea of programming languages like Python, JavaScript or even scripting can make a huge difference. Programming helps automate, understand vulnerabilities, and even create your own tools. When I first started learning programming, it helped me think logically and solve problems in a more structured manner.
In addition to programming, the operating system is also very important. As an ethical hacker, you will be working with different operating systems, especially Linux-based ones. Understanding the concept and the way an operating system works, as well as the way the system handles files, is very advantageous. I spent a lot of time working with different operating systems and this helped me feel comfortable while working with them.
In order to expand my impact and reach a wider audience, I founded Selkey Cyber Security Pvt Ltd.
Ethical hacking skills include web application security. The majority of the modern digital world is based on web applications and as such, they are often the primary target for cyber attacks. You need to have an idea of the construction of websites, the security mechanisms behind the login process and the potential security issues, such as SQL injection and cross-site scripting. In my case, the knowledge of web security helped me grasp the practical scenarios and the ways to avoid them.
Another skill to learn is problem-solving. Ethical hacking is not about using the correct procedure; it is about being creative. Every system is unique and each vulnerability is unique. You need to analyze the situation, try different things and find solutions. This skill is developed over time. I learned that sometimes the best solution comes when trying different things and not being too quick to give up.
Patience and persistence are also important skills in this field. There were many times when I spent hours trying to understand a problem or find a vulnerability without success. However, in ethical hacking, patience is a vital skill. You might not find everything right away and that’s perfectly fine. The important thing is to keep trying, keep learning and keep improving. Patience, after a while, turns into expertise.
The next skill that many people do not take into account is learning continuously. You see, the field of cybersecurity is changing every day. New vulnerabilities, new tools and new ways of attacking are being developed every day. If you do not learn continuously, you will be out of date. I developed a habit of keeping myself updated and learning new tools and new knowledge.
Equally important is the need to have a strong ethical mindset. The reason is that, as an ethical hacker, you are privy to sensitive information and systems. The question, however, is whether you are using the knowledge properly. From the very beginning, I was very clear in my mind that my intention was to protect and not to exploit. Ethics is what makes an ethical hacker and a cybercriminal different. Regardless of the level of expertise you acquire, ethics is what makes you who you are.
Another important skill is communication. The ability to explain technical issues in simple terms is crucial, especially if you are working with others or clients. There is a possibility of identifying vulnerabilities, but if you cannot communicate them effectively, you reduce your impact. I have been working on my communication skills to be able to effectively share my findings with others.
Lastly, the most powerful skill is the hands-on practice. While you can read books and watch tutorials, the actual learning comes when you put the skills into practice. Experimenting, testing and working on actual scenarios is what helps you gain confidence and skills. In my case, the most significant factor that helped shape my skills was the practical experience.
If I was to summarize everything, then I would say that if you want to become an ethical hacker, then it is not about mastering one skill, but rather about mastering a number of skills and having the right mindset. It is a continuous process of growth, learning and improvement.
So, if any individual wants to pursue this career, I would say, “Just start with the basics, be consistent and understand rather than memorize.” Do not hurry up! Start building your foundation gradually and always be ethical in your approach.
From my own journey in the world of cybersecurity, I have learned that skills take time, effort and dedication to develop and if you are willing to learn and have an inquisitive mind, you can make a great success out of the world of ethical hacking.
Contact With Me

Dhruvesh Panchal
Director & CEODhruvesh Panchal, founder of Selkey Cyber Security Pvt Ltd, promotes cyber awareness and digital safety through seminars and scam prevention initiatives.
Phone: +91 7777999564 Email: admin@dhruveshpanchal.com